Every web application development experts and security technologist should have a common understanding of web application security risks and how to deal with them. Software developers and security teams are frequently misguided along the way without an explicit deliberation of the security requirements and the associated security strategy for all possible security vulnerabilities. This is ineffective and often results in poor decisions and costly web application maintenance.
The web security infrastructure is one of the most important investments you can make in a software or web application. As an online business that provides a specific solution, you can't afford to lose customers through security issues such as data breaches, illegal data encryption, ransomware, and other related security risks. However, no matter how reliable your security strategies are, the possibility of your databases being compromised always exists.
There is no such thing as a bulletproof, perfect, and secured method for protecting sensitive data. Every successful web development security always keeps the user in mind. It's important to realize that the security plan doesn't just focus on the application but also on how users utilize the application.
Understanding Contemporary Security Models
The present-day web app security strategy standards can't always keep up with possible attack matrices. Security threats are constantly evolving, so you need a set of modern security practices not to fall behind. When you’re hiring or partnering to move faster, it helps to benchmark expectations against how top web application development companies typically structure secure delivery—so security requirements don’t get lost between internal teams and external collaborators.
Many developers and security experts assume that users will understand how to protect their accounts, such as using strong passwords and two-factor authentication, and even if they do, they will choose the most usable choice over the easiest one.
As developers and security technologists, security measures must be taken on the development side to secure users' sensitive information. It would be best if you did not assume that users will not do that for themselves. In context, the risk before addressing a threat will be higher than after addressing the threat.

Some of the popular misconceptions about security are listed below:
Users will always use the most secure choice
One of the worst assumptions is that users will be capable or willing to use the security standards that will best secure their data. The liability has to be on the web application security or web services to ensure that the data provided by users is hardened at minimum levels. As developers and security technologists, the most significant interest should be treating our user's data with the most respect you can provide.
Sanitizing data is not essential
Data is the most important resource that any online business owns. Many unexpected things can happen when developers build a form that fails to validate user input. Data can be sanitized by removing or replacing potentially harmful characters, such as using a whitelist or escaping the data input by the users. Remember, only correctly formed data should be allowed to be saved in the database.
Prioritize security at the cost of usability
While security is essential, you should not make the UI and UX suffer. Some of the main reasons for several online forms' abandonment include users being uncomfortable with the data input process. Many of these concerns can be solved through usability considerations. The concept of usability versus security must always be balanced.
Security will never be breached
The worst assumption a developer or security technologist could make is putting too much faith in its security standards and practices. Securing web applications and identification isn't about planning for the best, it's about preparing for the worst. There is no such thing as perfect or bulletproof security. Every system can be breached, and hackers can penetrate the system in just a matter of time. This is why all sensitive information should always be properly encrypted.
Web Application Security Threats
Security issues often arise as a result of several types of web security threats. Some are renowned, while some are new and complicated. Hackers or security attackers are constantly developing vigorous types of web application security threats to compromise sensitive data on the target database's web server and do even more malicious tasks. As a result, software developers and security experts are also counter-building solutions to vulnerabilities to strengthen their unsecured web service.

While the security threat varies depending on the type of web application and its complexity, the entire security risk relies on the process of protecting user data and risk assessment from potential security threat agents who are always looking for the application's vulnerabilities misconfigurations, and other security weaknesses. Understanding the web application environment is essential for keeping your data safe and, thus, the security threats to the data managed by the application.
Below is the list of the most common application security threats which are most known to security experts:
Code injection
Also known as Remote Code Execution. It is a type of attack that injects malicious code between a server and a client caused by processing invalid data. The web application interprets the injected code, altering how a program executes while the target may not even see the injected code.
Cross-site scripting (XSS)
A type of web security threat that enables a hacker or security attacker to inject malicious script into the output stream of the vulnerable web application through JavaScript or similar executable code. Cross-site scripting (XSS) usually occurs when hackers or security attackers send malicious scripts from a web browser to a different unsuspecting end-user without the option to identify the script which can lead to the execution of the malicious code.
Buffer overflow
The term is given for a type of security threat wherein an attacker exploits buffer overflow issues, including bypassing the programming languages standards and overwriting the memory of a web application. This can be done by manipulating memory and triggering a response to inflict damage on the files and enabling hackers or security attackers to perform impossible tasks because the affected memory contains executable code.
Session hijacking
Also known as TCP session hijacking. It's a type of security attack wherein a hacker or security attacker takes over a web user session, including the authentication and access control consent, and disguises as the authorized user. A session hijacker bypasses the network security and enters the session through data interception between the user and the web server. Cookies, URL rewriting, and hidden fields are three common places to look for information used to hijack a session.
SQL injection
The term is used to describe attacks that modify a malicious database query that your web application creates as the result of user input. Similar to code injection, particular code is being added but in SQL format instead, which can involve the use of escape or other unexpected characters via the input data from the client to the application. A hacker or security attacker can often modify, delete data or execute administration operations, resulting in persistent modification to the web application's content or behavior.
Remote Code Inclusion
Also known as RFI. It is a type of security threat that targets applications dynamically referencing external scripts. The majority of web applications rely on pre-installed libraries, frameworks, and APIs. The attacker's goal is to compromise the referencing function from the external resources and upload malware that can later be used as a backdoor. This enables the attacker to get authorized to circumvent standard security measures and gain high-level user access. To make it easier to modify the location of the remote code later, the include statement frequently contains a relative path or uses a variable containing a hardcoded path.
These web security threats can have a significant impact on different sizes and types of applications if you search long enough online. In that case, you could discover more lists and not even begin to scratch the surface of how a hacker or security attackers can make it more challenging to secure web applications these days. As securing web apps progresses, you'll encounter a much larger number of threat types and start to build security standards and practices to overcome them.
The purpose of the web application is to interact with data safely. Web application development is the process of creating a series of programs that can interact with a database or schema. It's often hosted on a remote server that can be accessed through the user's device on a network over the internet through a web browser such as Google Chrome, Mozilla Firefox, or Safari.
Secure Web App Development Best Practices
Developing a secure web application is like building a house. To build a house, you must first lay a solid foundation and add all of the features such as roof, windows, doors, and so on. Of course, the process doesn't stop there. As a builder, you should install locks on the house to prevent strangers from breaking in and wrecking it while continuously monitoring potential external threats. How strong or weak the locks are determined by how clearly they can eliminate risk in the realm of web application security.
As software developers and security technologists, it's now possible to offload knowledge about identity and data security by understanding how to properly obscure data in transmission and identify the key classes of web application vulnerabilities and the business risks they pose through various web applications security best practices.
Despite this awareness, there is no such thing as bulletproof security. From startups to massive corporations, no one is immune from being targeted. To improve the overall quality of security on web applications, below are some of the web application security best practices that you can apply to your development process:
Conduct security testing regularly. The goal of web application security testing is to identify any security threats or vulnerabilities in a web application and its environment, document those security threats, and provide solutions to fix them. There are various static application security testing methodologies. Web application security audits, vulnerability assessments, and penetration testing are examples of these. Depending on the type of threat, these may differ in their scopes and objectives and can be executed with different levels of automation.
Build preventative countermeasures. Most of the vulnerabilities discussed in this article could have been avoided simply by not allowing them to occur. The best way to avoid creating vulnerabilities is to incorporate security into the development cycle itself. Security should be embedded at all stages of web application development, including in the planning stage, coding, http strict transport security test, user management, and testing both during and after development. The preferred method of vulnerability management is prevention, which is one of the keys to secure web applications.
Design data security encryption. Data security isn't just about planning but preparing for unexpected attacks. If something is possible, you should assume that it will happen and have a plan to reduce or mitigate the security damage. Data encryption is not just about preventing data from being stolen, it can also slow down the process for hackers to make it infeasible for them to decrypt massive amounts of data. The key to a prevent hackers from data theft from your application is to use encryption to transmit data of any sort between two endpoints to help keep hackers from listening in on your communication. To secure a web application, it's vital to keep track of the latest encryption techniques and rely on the best encryption supported by the user's environment.
Manage web applications through third-party resources. One-size-fits-all web applications no longer exist in this information age. Most modern web applications interact with online data sources and rely on third-party assets such as libraries, APIs, and microservices. It is never a good idea to reinvent the wheel, especially with web application development. Some developers may have already developed a security solution that meets your security requirements. While third-party solutions can positively and negatively affect your application, they must be considered in your security plan so that others know that you have a solution in mind that is already working on others. However, the web application development and security team must ensure that they maximize their legal leverage over their third-party software vendors to provide all security features and timely upgrades/patches.
Constantly get updated with the latest security measures. Securing web applications is a progressive process involving the application owners, end-users, the development team, and the security team. It is vital to continuously update yourself with the latest technologies, security checklists, and methodologies and understand the key differences and relationships between security threats, vulnerabilities, breaches, risks, and countermeasures.
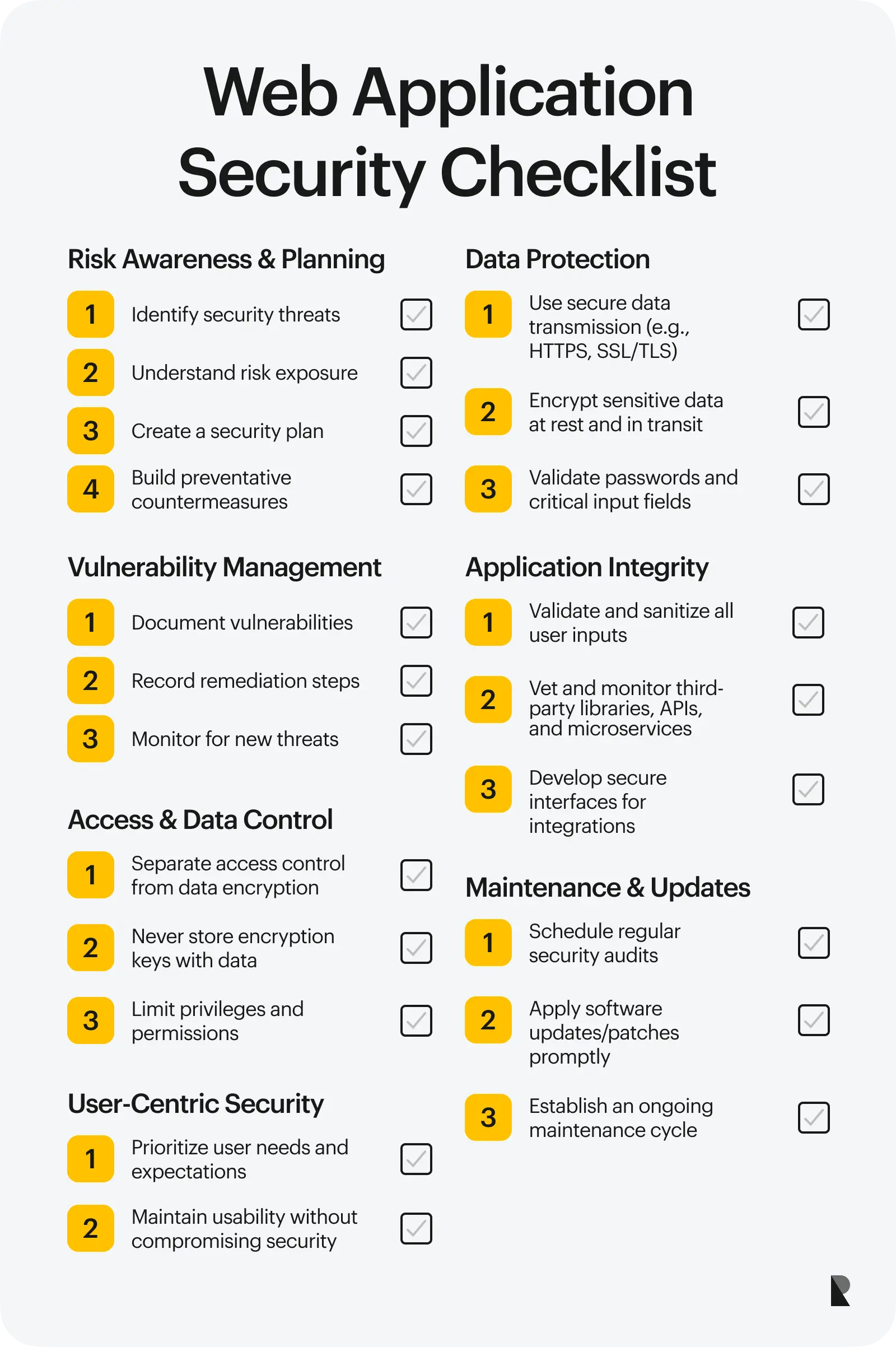
Web Application Security Checklist
Web applications can and do break at times. Every software is constantly exposed to several security threats online, and so is every code your application uses. In that case, you must maintain and upgrade your application regularly to reduce the risk of known security threats.
If you wish to secure your web application, follow these web application security checklist below:
Wrapping Up
Building a secure web application is not an easy task. Security is always about utilizing control over data at rest and in motion. The web application must maintain control over the manner in which it interacts with data and the web server itself. Managing data, conducting a threat assessment, securing data transmission, and creating a maintenance cycle are all part of the big picture of web application security.
This article taught you how to secure your web application and ensure that users' data are safe and protected.
Jun 22, 2022
