Introduction
The web comprises many parts and pieces that work together and often communicate with each other. These pieces are the webpages, the servers where they are hosted, the backend software that those servers run, and third-party APIs that might be connected to them.
When these pieces communicate, they need to discover each other's identity to know whether they can trust one another before they begin corresponding. This is especially important when one piece is on one server and speaks a different language (or protocol) than the other piece.
Cross-Origin Resource Sharing (CORS) is a protocol allowing foreign server pieces to communicate. This guide will cover what CORS is, how it works, how it benefits you and your website security, and how you can enable CORS on your websites if it still needs to be enabled by default.
The same origin policy is a crucial web security mechanism that prevents malicious access to resources from multiple origins. However, it also contains legitimate cross-origin requests, limiting the functionality of web applications.
Cross-origin resource sharing, or CORS provides a way around this limitation by enabling restricted resources to be requested from different origins. Using HTTP headers, CORS allows servers to specify origins that can access resources, allowing cross-origin communication and enabling new functionality in web applications.
It's important to remember that CORS is not a security mechanism; it simply allows communication between different origins. Many leadership teams get better outcomes when CORS is designed as a cross-functional control—co-owned with security and delivery collaborators (including web and app development companies), so velocity doesn’t quietly outpace governance. Allowing cross-origin requests can open up many new web application possibilities and increase the attack surface.
Defining CORS
What is cross-origin resource sharing?
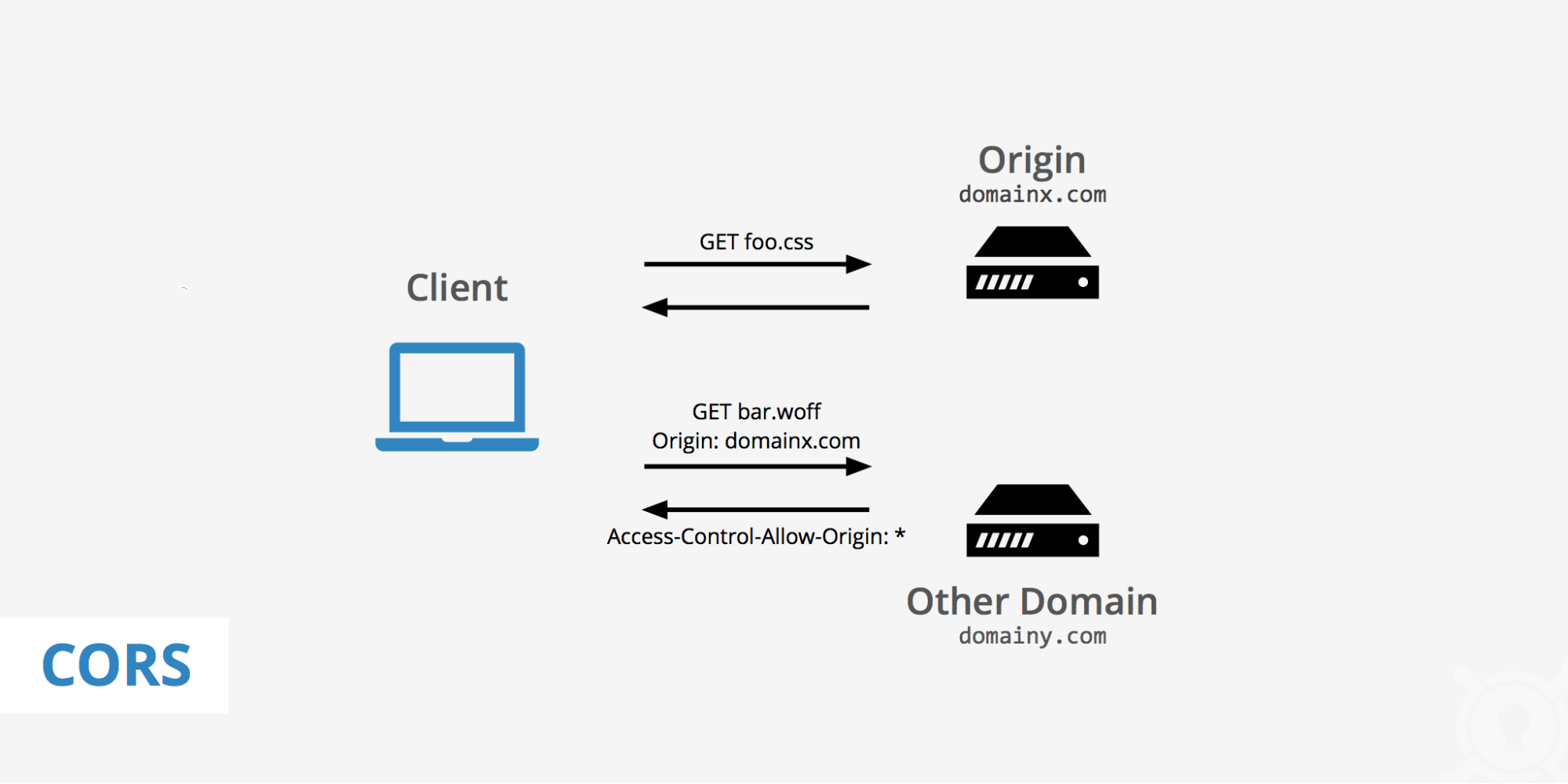
Cross-Origin Resource Sharing (CORS) is a mechanism that allows restricted resources (e.g., fonts, JavaScript, and CSS files) on a web page to be requested from another domain outside the domain from which the resource originated. In other words, it's a communication between domains in different URLs.
This is done by adding a request header that contains the appropriate access list of domains allowed to access the resource. The server then uses this information to decide whether or not to send the requested resource.
The CORS specification is implemented in the browser and server, allowing web applications to make cross-origin requests. The specification also defines how a browser should handle these requests and how servers should respond.
CORS is an essential feature for web app developers because it allows them to build rich web applications with full cross-domain support. However, CORS has some limitations which prevent it from being used in certain situations.
For example, if you want to use JavaScript to access a resource from another domain, you can only if the server explicitly enables it.
Understanding CORS
Cross-origin resource sharing (CORS) is a mechanism that uses additional HTTP headers to indicate which resources are to be shared with the requesting origin. CORS is implemented by web browsers, web servers, and web application frameworks.
CORS was designed to allow cross-origin HTTP requests in situations where they might otherwise have been blocked by browser security features. If a browser were to block such requests, it would not be possible to use AJAX across subdomains or make XMLHttpRequests between domains.
CORS works by allowing the server to indicate which methods and headers can be used when requesting the resource. It also allows the server to indicate whether certain response headers can be accessed from any domain, or if they should only be accessible from certain domains (e.g., a response header indicating an authorization status).
Same origin policy
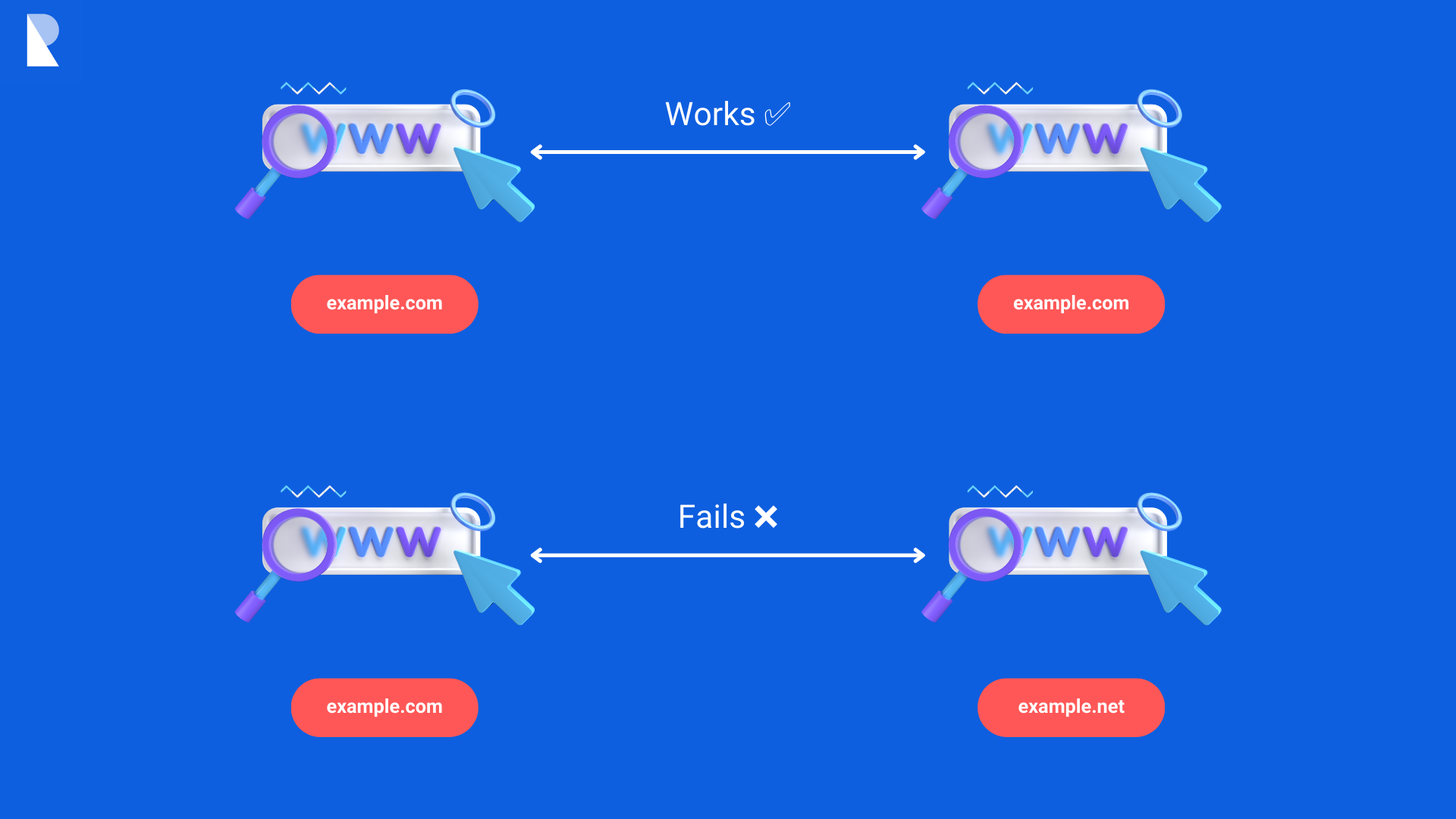
To understand CORS, you must know about the Same Origin Policy (SOP). This is an important security feature of browsers that restricts scripts from accessing data on other domains.
For example, if you're viewing a site that contains an embedded map from Google Maps, the map will work fine. But if you try to embed another website's map on the same page, it won't work because browsers block this behavior by default due to SOP restrictions.
The same origin policy is a security feature that prevents scripts from one origin from accessing data from another origin. In other words, it prevents cross-site scripting (XSS) attacks by limiting the reach of JavaScript code.
The same-origin policy is important to web browser security because it prevents websites from accessing sensitive data or functionality on other sites.
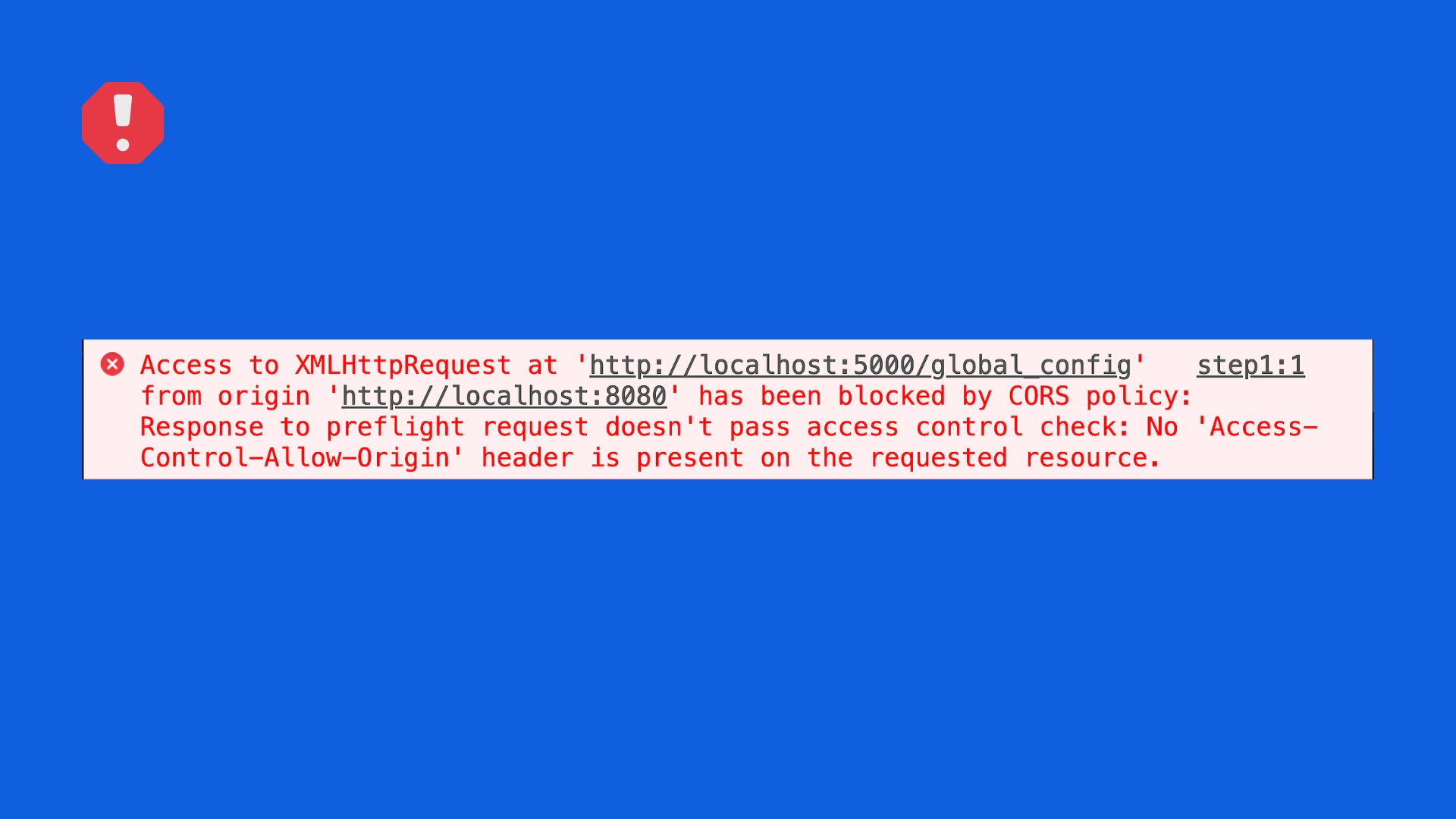
Example CORS error:
When a web browser processes a page, it will generate a list of all the resources used to display it. This includes images, stylesheets, scripts, and other files. The same origin policy says that if two sites are loaded from different domains, they can't share requested data using JavaScript.
In short, the same origin policy:
- Prevents access to resources from different origins
- Ensures security and data integrity
- Applies to: XMLHttpRequests, Web fonts, CSS stylesheets
Cross-origin resource sharing (CORS)
The same-origin policy is a security measure preventing scripts from reading, modifying, or transferring data to other domains. It was created to protect users by preventing malicious websites from stealing and using your information in harmful ways.
But sometimes, you want to allow cross-origin requests, such as when you want to load data from another website or make an AJAX request. This is where cross-origin resource sharing (CORS) comes in.
CORS is a mechanism that allows restricted resources from another domain to be accessed by a web application, with some limitations.
The CORS specification defines a way for browsers to make cross-domain requests on behalf of a web application. This is done by adding an HTTP header specifying which domains can send requests. By default, most browsers allow requests to only come from the same origin as the resource being requested.
So, in short, CORS:
- Allows restricted resources to be requested from different origins
- Uses HTTP headers
The Mechanics of CORS
Several steps occur when a website uses CORS:
1. Browser sends OPTIONS request (preflight request)
A browser sends an OPTIONS request to check if the server supports CORS. This is called a preflight request and is sent before any actual post requests are made. If the server does not support CORS, it will respond with a status code 405 (Method Not Allowed).
If the server supports CORS, it will respond with a 200 (OK) status code. The response will contain an Access-Control-Allow-Origin header. This header lists origins that are allowed to make requests to this resource.
2. Server responds
The server receiving the preflight request must respond with appropriate CORS headers that allow or deny the actual cross-origin request. The server can include the following headers in its response:
- Access-Control-Allow-Origin: Specifies the allowed origin(s) for cross-origin requests. The value can be a specific origin or "asterkis" to enable any origin to (not recommended for sensitive data).
- Access-Control-Allow-Methods: Lists the allowed HTTP methods for the actual request.
- Access-Control-Allow-Headers: Lists the allowed headers for the actual request.
- Access-Control-Allow-Credentials: Specifies whether the browser should include credentials (cookies, HTTP authentication) in the request.
- Access-Control-Max-Age: Specifies how long the preflight response can be cached, reducing the need for frequent preflight requests.
- Additional headers depending on the request.
3. The actual request is sent, and a response is received.
The response is checked for an Access-Control-Allow-Origin header; if it's present, the request can proceed. If not, a "preflight fail" error is returned, and the actual request doesn't happen.
Key Components of CORS
The CORS headers are a set of headers that can be used to enable cross-origin resource sharing (CORS) in web browsers. The World Wide Web Consortium (W3C) specifies the Cross-Origin Resource Sharing specification headers.
The following are the main components of CORS:
1. Access-Control-Allow-Origin:
Purpose: Specifies which origins are allowed to access the resource on the server.
Value: The value can be a single origin (e.g., https://example.com) or * to allow any origin. Due to security concerns, * is not recommended for sensitive data.
Example
Access-Control-Allow-Origin: https://example.com2. Access-Control-Allow-Methods:
Purpose: Lists the HTTP methods that are allowed when making cross-origin requests.
Value: A comma-separated list of HTTP request methods (e.g., "GET, POST, PUT").
Example:
Access-Control-Allow-Methods: GET, POST, PUT3. Access-Control-Allow-Headers:
Purpose: Lists the HTTP headers that can be included in the request.
Value: A comma-separated list of allowed headers (e.g., "Content-Type, Authorization").
Example:
Access-Control-Allow-Headers: Content-Type, Authorization4. Access-Control-Allow-Credentials:
Purpose: Indicates whether the browser should include credentials (such as cookies or HTTP authentication) in the cross-origin request.
Value: "true" if credentials are allowed, "false" if not.
Example:
Access-Control-Allow-Credentials: true4. Access-Control-Expose-Headers:
Purpose: Specify which headers can be exposed to the requesting client.
Value: A comma-separated list of headers the server allows to be exposed.
Example:
Access-Control-Expose-Headers: X-Custom-Header5. Access-Control-Max-Age:
Purpose: Specifies how long the browser can cache the results of a preflight request (the OPTIONS request).
Value: The time, in seconds, that the preflight response can be cached.
Example:
Access-Control-Max-Age: 3600</code>`</p>6. Access-Control-Allow-Origin (in Preflight Responses):
Purpose: Similar to the regular Access-Control-Allow-Origin, this header is included in the response to a preflight request.
Value: Specifies the allowed origin for the preflight request.
Example:
Access-Control-Allow-Origin: https://example.comImplementing CORS
Enabling CORS on an origin server involves configuring the server to include the appropriate CORS headers in its HTTP responses. Below, you can see how to enable CORS for a simple example using different programming languages and frameworks. Keep in mind that specific configurations may vary based on your server setup.
Express.js (Node.js)
Install the cors middleware package:
npm install corsIn your Express.js application:
const express = require('express');
const cors = require('cors');
const app = express();
// Enable CORS for all routes
app.use(cors());
// Your routes and other middleware
const PORT = process.env.PORT || 3000;
app.listen(PORT, () => {
console.log(`Server is running on port ${PORT}`);
});Flask (Python)
Install the flask-cors package:
pip install flask-corsIn your Flask application:
from flask import Flask
from flask_cors import CORS
app = Flask(__name__)
CORS(app) # Enable CORS for the entire app
# Your routes and other app configurations
if __name__ == "__main__":
app.run()ASP.NET Core (C#)
In ASP.NET Core, CORS is configured in the Startup.cs file.
In your Startup.cs:
using Microsoft.AspNetCore.Builder;
using Microsoft.Extensions.DependencyInjection;
namespace YourNamespace
{
public class Startup
{
public void ConfigureServices(IServiceCollection services)
{
// Add CORS services
services.AddCors(options =>
{
options.AddPolicy("AllowAllOrigins",
builder =>
{
builder.AllowAnyOrigin()
.AllowAnyMethod()
.AllowAnyHeader();
});
});
// Other service configurations
}
public void Configure(IApplicationBuilder app)
{
app.UseCors("AllowAllOrigins");
// Other middleware and configurations
}
}
}Django (Python)
Install the django-cors-headers package:
pip install django-cors-headersIn your Django application's settings.py:
INSTALLED_APPS = [
# ...
'corsheaders', # Add this line
# ...
]
MIDDLEWARE = [
# ...
'corsheaders.middleware.CorsMiddleware', # Add this line
# ...
]
CORS_ALLOWED_ORIGINS = [
"https://www.example.com", # Add your allowed origins here
]
# Other settingsThese are some examples that can help you enable CORS in various frameworks. It's important to remember that you'll need to customize the CORS configuration to meet your specific needs. This includes specifying allowed origins, methods, headers, and credentials.
Improperly configured CORS settings can put your application at risk for security vulnerabilities and other issues. You should fully understand the implications of any configuration setting you apply, so test each change thoroughly before going into production with it.
CORS in Practice
Let's consider a real-world example of a web application hosted on one domain (https://www.example.com) that needs to fetch data from an API hosted on a different domain (https://api.exampleapi.com). We'll use JavaScript to make cross-origin requests using the Fetch API.
Here's how you can implement CORS in practice:
Server-side (API) Configuration:
Assuming you control the API server, you must configure CORS headers to allow requests from the web application's domain.
For Node.js with Express.js:
const express = require('express');
const cors = require('cors');
const app = express();
// Enable CORS for the weather API
app.use('/weather', cors());
// Define the weather route
app.get('/weather', (req, res) => {
const weatherData = { temperature: 25, condition: 'Sunny' };
res.json(weatherData);
});
const PORT = process.env.PORT || 3001;
app.listen(PORT, () => {
console.log(`API server is running on port ${PORT}`);
});Client-side (Web Application) Implementation:
In your web application hosted at https://www.example.com, you can use JavaScript to fetch weather data from the API using the Fetch API.
// Fetch weather data from the API
fetch('https://api.exampleapi.com/weather')
.then(response => response.json())
.then(data => {
// Display weather information on the web page
const temperatureElement = document.getElementById('temperature');
const conditionElement = document.getElementById('condition');
temperatureElement.textContent = `Temperature: ${data.temperature}°C`;
conditionElement.textContent = `Condition: ${data.condition}`;
})
.catch(error => {
console.error('Error fetching weather data:', error);
});In this example, the CORS configuration on the API server (https://api.exampleapi.com) allows requests from any origin by using app.use('/weather', cors());. The web application hosted on https://www.example.com makes a cross-origin request to fetch weather data using the Fetch API.
When the browser sends the request to the API, it includes the Origin header indicating the requesting origin (https://www.example.com). The API server responds with appropriate CORS headers, such as Access-Control-Allow-Origin: *, which allow the browser to access the response data. The web application then processes and displays the weather information retrieved from the API.
This example demonstrates how CORS enables controlled access between a web application and an API, allowing the application to fetch and display data from a different domain while maintaining security and privacy.
Best Practices and Potential Vulnerabilities
There are several best practices you can use to enhance your security and efficiency when using CORS:
- Use preflight requests. Preflight requests allow your server to determine if it can respond appropriately before actually performing the request. If a preflight request fails, the browser will not send the actual request. This prevents unauthorized cross-domain requests from being made by malicious users or bots that might attempt to abuse your website.
- Don't use wildcard origin requests. Wildcard origin requests allow you to specify that any origin can make a request, which raises Content Security Policy (CSP) violations by malicious websites or bots attempting to perform cross-domain requests.
- Set headers appropriately. Set headers such as "Access-Control-Allow-Origin" and "Access-Control-Allow-Headers" appropriately so that you don't accidentally expose sensitive information about your application or users through these requests.
CORS is a powerful tool to enhance security and efficiency. However, it is also a potential source of vulnerabilities.
Misconfiguration and lack of awareness about the security implications of CORS can lead to severe exposures. The above best practices can help protect your application from malicious attacks.
Conclusion
Though implementing CORS is not very difficult, it can still be confusing if you haven't used it before. The above steps should help you start configuring your sites with CORS and enable you to get set up with CORS similarly.
Reading this article has helped to clarify how CORS works and how to implement it on your site. So go ahead and give it a shot!
CORS has become an increasingly important part of web development, but there are potential security concerns that you must also be aware of. Putting myself and other experts out of work is essential to implementing CORS properly.
If you follow the advice above and study how CORS works, you should have a solid grasp of how it can help your applications function more effectively.
CORS has been a significant development in web security. The ability to use the same domain between different domains will, in time, become an essential part of new app development strategies. From a development perspective, CORS is a crucial piece of the puzzle that made the modern single-page application possible.
However, it can introduce security risks if not configured properly, and like any other tool, it should be used with caution. Your best bet is to work closely with an experienced web development company if you need help with CORS implementation.