Introduction
What is website defacement?
Website defacement is a known security vulnerability where hackers gain unauthorized access to a website or web page and drastically modify the visual appearance or content through malicious or suspicious code.
Websites and their supplementary data will always have significant economic value. Information has become an essential resource for individuals and businesses more than ever. Companies collect and analyze vast amounts of information on the web to gain insights, create informed decisions, and develop targeted marketing strategies. Nonetheless, both websites and their auxiliary data are also the primary motivation for many hacktivists ranging from ideological purposes to personal amusement or showcasing their hacking skills.
According to IT Governance, 104 publicly disclosed security occurrences accounted for 277,618,767 leaked records. This reported data has increased to what they documented in any calendar month last year. It only proves that there has been substantial commentary on the role of cyberattacks that draws on various data sources and increasingly prevalent threats in today's interconnected world.
These growing attacks target businesses and individuals seeking to exploit vulnerabilities in technology systems and networks for various purposes, including financial gain, espionage, defacement, or even disruption.
Some of these cyber-attacks will sound very familiar. Other assaults may be unpredictable or unfamiliar simply because they do not appear on a popular list of vulnerabilities or recently reported cyber attacks. Ransomware, defacement, distributed denial-of-service (DDoS) attacks, and security breaches are just some of the nightmares of website developers and administrators, which can cause significant harm to applications and the associated data.
Adding to the burden, the catastrophic results of any mistake could haunt you for the rest of your career. That’s why many executive teams choose to work with experienced build partners, sometimes by shortlisting the best website development companies, to validate security assumptions early (access control, deployment hygiene, and content integrity) before small gaps become brand-level incidents. The potential consequences of a security incident can far outweigh the efforts and investments required to implement proper security measures.
While you can find various lists of web application threats all over the web, some are comprehensive and don't necessarily have a bias. Several lists address what the author thinks are the most critical threats; some tell you about the most common hazards on many websites. Among these threats, one severe attack that can inflict on a website is a type of website vandalism called defacement.
This involves malicious parties infiltrating a website and altering its visual appearance or informational site content. Defacement attacks often involve adding inappropriate content of a social, religious, or political ideology which can be an unrelated text that deviates from the site's subject matter.
If a website has been compromised or hacked, one unmistakable sign is web defacement. This attack involves infiltration by unauthorized administrative access who commits digital vandalism. Modifications to the website's visual appearance or content are apparent. Compared with other attacks, hackers and hacktivists leave their contact information or name behind to associate themselves with the defacement.
As a website owner, if you discover that your homepage has been replaced with something that isn't your original design and existing content, you have likely fallen victim to website defacement.
This all-inclusive article will examine website defacement attack as a brutal act of website vandalism. The causes for website defacement attacks, its effects and consequences, and effective measures for defacement prevention and detection shall be explored.
We will discuss post-defacement measures to secure websites or web applications in a few points to view this threat from the perspective of potential adversaries, enabling us to identify security vulnerabilities that can go deeper than defacement and alter important core files.
Defining Website Defacement
When hackers gain access to a web server infrastructure or content management system (CMS), they can replace the original content with their digital content through file uploads and add malicious files or source code.
A defacement attack compromises the website's integrity and can have various motivations, including spreading false messages, swear words, promoting ideologies, and significant disruptions. Attackers who deface websites are referred to as defacers. Defacers can be compared to graffiti artists painting your website's wall and leaving a signature to show off their hacking skills.
How does website defacement happen?
A widely accepted fact is that website defacement attacks happen due to unauthorized changes in a website's visual presentation or content. Nevertheless, more behind-the-scenes schemes are connected to a vandalized website. This involves utilizing hacking technologies, cross-site scripting methods, and file uploads with malicious code or any means of exploitation.
Common causes of website defacement include:
Unauthorized access
This occurs when defacers gain access to a website through underlying means such as exploiting weak passwords, compromised user accounts, server configuration, or unpatched software vulnerabilities. Upon unauthorized entry into your website, defacers limit access, manipulate its visual presentation, and exploit any uploaded files.
SQL injection
A typical attack uses source code or malicious SQL code to exploit vulnerabilities in backend databases. This enables user-driven data (including sensitive company and private user data) to be directly included in SQL queries without proper sanitization. Accessing the database can help hackers deface websites through unauthorized database account information manipulation.
Cross-Site Scripting (XSS)
An injection attack where potential defacers inject malicious scripts into a website's or application's code. This can then be executed on the browser of the users and can be used to bypass security mechanisms to send malicious code on behalf of the visitors. Through this malicious intent, the hackers deface websites in various ways as needed.
DNS hijacking
This is another vicious website defacement attack involving gaining unauthorized control over a website's Domain Name System (DNS) through DNS queries to redirect users to malicious sites. Website defacers can then deface the website hosted on the redirected server and display their preferred political or personal ideology content.
Malware infection
Websites typically need integration software outside their core ecosystem, which can be a doorway for malware infection. Through bot management technology and malicious scripts, a standard payload can help defacers insert malware as backdoors and gain administrative access to modify the website's content to display their defacement message.
Real-World Website Defacement Attacks
If you're wondering what website defacement looks like, here are some of the notable real-world instances of website defacement attacks:
Twitter Defacement Attack

In 2009, the official Twitter website by the 'Iranian Cyber Army,' an unknown group. Even though the website defacement attack indicated no links with Iran authorities, the Farsi poem on its page suspects that these are Iran's Islamic system of rule due to the nature of the message. The homepage went all black with a green flag and red lettering in English: "The Iranian Cyber Army has hacked this site." This message criticized Twitter's role in the Iranian election protests then.
Microsoft Defacement Attack
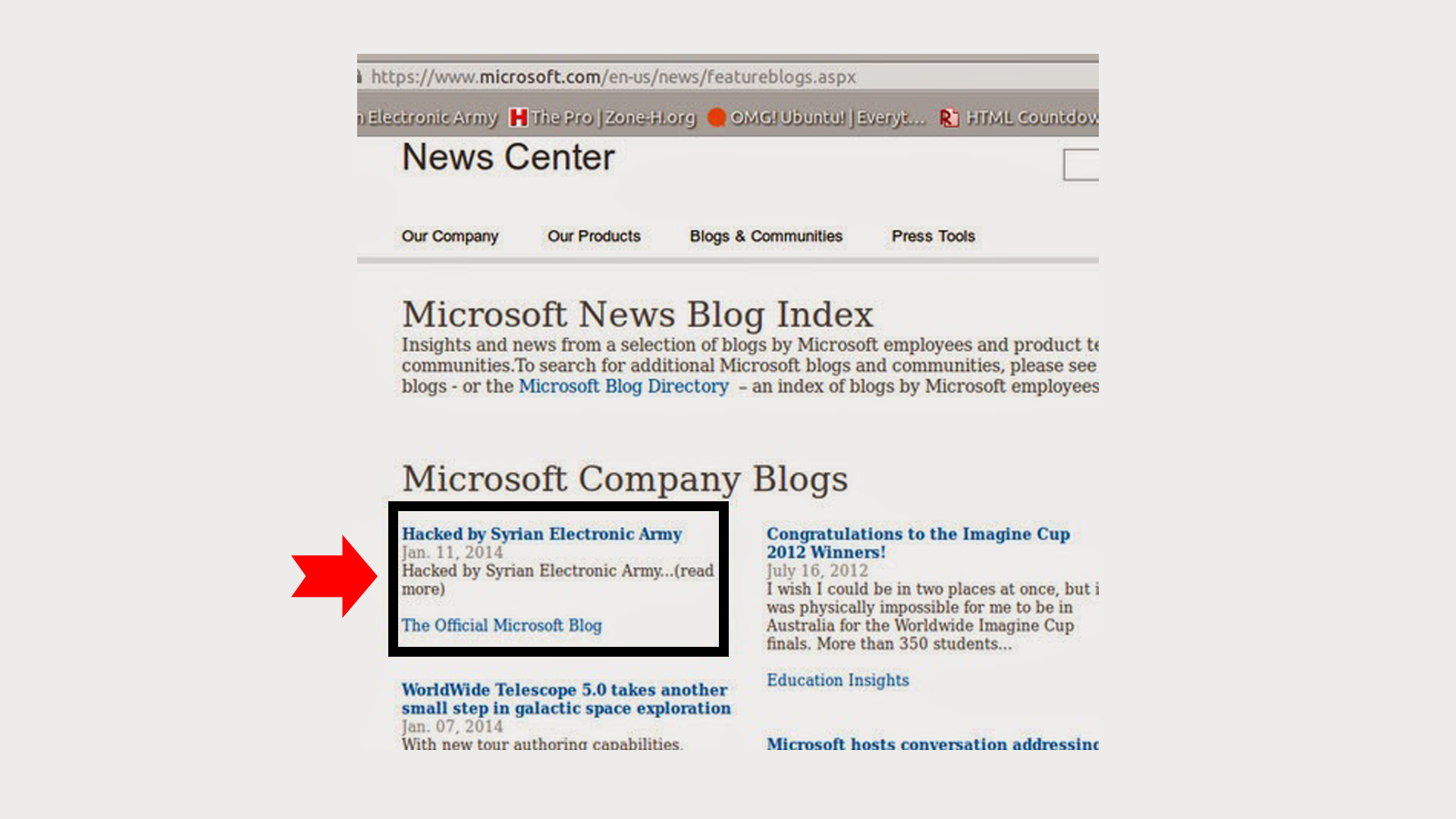
In 2014, the Syrian Electronic Army hacked several high-profile Twitter accounts and websites, including Microsoft's official blog and Twitter account. Though the Syrian group claims to be hacking in support of Syria's Assad regime, they hacked various websites to post oddly juvenile announcements with messages such as "Exclusive! Justin Bieber to E! online: I'm a gay") to primary vandalism ("Syrian Electronic Army Was Here"). The website defacement attack messages expressed political opinions and criticized the UN's stance on specific issues.
NHS Defacement Attack

In 2018, the NHS website hosting data from patient surveys operated by UK National Health Service (NHS) was defaced by unknown attackers. The landing page of insights.london.nhs.uk was modified to a black background, eerie music, and a message that read "Hacked by AnoaGhost.". A Cybersecurity expert, Kevin Beaumont, tweeted a screenshot of it to his followers—a cached screenshot of the web page online claims that it had been defaced for almost five days.
The Motives Behind Website Defacement
Hacktivists often hack websites and persist in similar attacks to get some value from their work. Although some hackers are after financial rewards, website defacements can encompass various exploitative actions. On occasion, defacers utilized diverse approaches such as bot traffic, altering traffic headers, and breaching web application firewall to demonstrate their expertise and imprint a presence on a website.
Below are some common reasons why attackers engage in website defacement:
Attention Awareness
A subset of website defacement attackers enables defacers to achieve greater visibility and generate interest in their actions. The goal is to create awareness and leave a digital 'signature' or communicate a message to a vast audience within the briefest timeframe achievable.
Political Ideologies
Most widely known website defacement attacks involve protests against particular political views or governments to express their political or ideological beliefs. Hackers target websites of government institutions, political organizations, or entities that may be associated with them and display messages on their websites. Website defacement can serve as a platform for digital protest or activism for certain hacker groups.
Revenge
Occasionally, website defacement attacks are motivated by personal grudges or a desire for revenge. Defacers may attack website administrators who work for companies or organizations that haven't paid them. Defacing their websites may cause embarrassment, disruption, or damage their reputation.
Demonstration of Hacking Skills
Hackers sometimes want to showcase their hacking powers or gain recognition within the hacking community. Having some recognition can help them gain some hacker identity in the community to attract attention from like-minded individuals.
Security Vulnerability Awareness
Some hackers may deface a website to raise or expose particular vulnerabilities in a website's security. Defacing a website can highlight specific exploitation opportunities or flaws in the website's defenses.
For Fun
Some website defacements are only done for fun and kill time. While defacement attacks are considered illegal and unethical, hackers may do it to mock the site administrators for the sake of fun.
The Impact and Consequences of Website Defacement
If you find yourself caught up in a website defacement nightmare, the real consequences for your business or brand can be severe. These consequences can be physical and abstract effects that may target the current security posture and the people using your website.
When defacers attack your website, your visitors and potential customers discover that you might not have the thorough commitment to quality of services they expect you to offer them. Regardless of the technique used in the attack, whether it's sending malicious traffic, DNS hijacking or malware infection, the vulnerability exploited by hackers can inflict severe damage on both your end and the user's end.
The following are the potential aftermaths of the website defacement attacks:
Financial Loss
The most significant effect of a defaced website is the loss of profit. The duration of the website's unavailability may cause you a huge amount of profit, affecting both your users and your business.
An inactive website with an unknown message displayed on it may lead to a loss of online sales, customer trust, or business opportunities. In addition, the cost of website restoration from hackers and adding security layers to address the ongoing security vulnerabilities may be expensive as it may re-occur if not given thorough attention and solution.
Negative Brand Reputation
One intangible effect of website defacement is damaging the targeted entity's reputation. Users trust that you test your website to ensure they function correctly and are safe to use.
When your website gets defaced, and your website displays a negative message, whether it's a political or personal ideology that is not aligned with what your brand is known about, visitors, clients, and stakeholders potentially lose trust in your business's ability to protect sensitive information or prevent attacks online presence.
Business Disruption
Aside from financial loss, a defaced website can disrupt the normal day-to-day operations of a business. This can lead to interruptions of your services and potential financial losses, especially for e-commerce websites that rely heavily on their website's availability and functions.
Psychological Damages
Due to its nature, website defacement can psychologically impact both users and the website administrators responsible for maintaining the website. This can affect both the morale and confidence of the involved individuals as it may inflict violation, frustration, and vulnerability.
How to Prevent Website Defacement
Taking different security precautions can lower the chances of websites getting compromised. These measures would help to prevent any website defacement opportunities and eliminate common vulnerabilities:
1. Implement strong user authentication
Utilizing a secure user authentication process with two-factor authentication (2FA) enables users and administrators to employ individualized, intricate passwords, thus fortifying the security of identity and access management programs.
2. Choose secure hosting
Subscribing to a trustworthy and safe hosting provider significantly diminishes the vulnerability to hacking incidents. This is achieved by implementing robust security protocols, including firewalls, intrusion detection systems (IDS), and frequent backups.
3. Update software regularly
Software functions as the underlying operating system for websites. Enhancing protection against defacement attacks can be achieved through regularly updating your content management systems (CMS), plugins, source codes, themes, and server software with the most current security patches.
4. Enable SSL/TLS
SSL certificates keep users' data secure and ensure all interactions are encrypted. In addition, it can validate ownership to avert the establishment of counterfeit website versions and hinder defacement attacks.
5. Control File Uploads
Taking proactive steps such as restricting file uploads and integrating comprehensive control mechanisms can fortify your system against potential breaches caused by hackers. Securing your system involves determining permission levels for different file types, validating uploaded file extensions, and conducting virus scans.
6. Limit modal and error messages
The disclosure of highly detailed error reports on your website might indicate areas of weakness that hackers can exploit to target specific potential vulnerabilities. Ensure you only display minimal error reports or messages to avoid any possible threat.
7. Sanitize HTML inputs
OWASP recommends implementing HTML sanitization as a security measure to prevent XSS vulnerabilities. Sanitization contains a security mechanism to remove unsafe characters from untrusted raw HTML strings before submitting them to your database.
8. Bot Management
Managing bots lets you filter which bots can access your website's resources. Some defacement attacks are caused by bots that are not filtered. Bot management allows you to utilize valuable bots like Google bots to block malicious or unwanted bots from penetrating. This can involve static inspection of traffic headers, revealing bot traffic, and asking bots to process JavaScript and CAPTCHA.
How to Recover a Defaced Website
Recovering a defaced website is a significant task. But how can you do that? The following are the measures to take to recover a website from a malicious defacement attack:
- Begin by signing in to the server using one of the following methods: SFTP, SSH, or Cpanel.
- Generate a backup of the website's current state. This process entails creating a duplicate copy of all relevant files and data to ensure their preservation in case of unforeseen events or issues.
- Switch the website into maintenance mode and temporarily suspend user access.
- Proceed with identifying any recent modifications made to files on the server. Thoroughly examine file records and metadata to pinpoint changes within a specific timeframe.
- Determine the severity of the attack by assessing the impact on the website. Analyze the affected pages and evaluate the extent of the damage inflicted, such as data corruption, loss of site functionality, or unauthorized alterations.
- Conduct a comprehensive server scan to detect potential backdoors—undisclosed points of entry—and promptly remove any identified malicious source codes.
- Thoroughly inspect the server logs to ascertain the entry point and identify the specific vulnerability exploited by the defacer. Analyzing the records will help you understand the attack's origin and highlight the security loophole that allowed unauthorized access.
- Restore unverified CMS (Content Management System) system files by replacing them with new copies from the initial setup.
- Perform a meticulous examination of the website's source code to identify any suspicious codes that may have been injected.
- Initiate a thorough cleanup and maintenance process for the website.
- If your website's ranking has been negatively affected by the attack, consider requesting a Google review to have the website unflagged. This can be done by contacting Google's support or review team to rectify any detrimental impact on your website's visibility and ranking.
Final thoughts
Website defacement is a severe security attack that alters a website's original form and content. The reason for defacements may vary from social, religious, or political nature and can seriously inflict physical and psychological damage to both users and site owners.
While no one wants to fall prey to defacement attacks, it can be reduced through standard security measures such as regular backups and updates, controlling file uploads, doing security checks, etc. Identifying the source of the defacement attack right after it happens is critical to avoid further damage.
Jul 11, 2023
